Users
Core functionality of Loft is giving other people self-service access to Kubernetes clusters. Everyone who should get access to a Kubernetes cluster, must be an authenticated user in Loft.
Working with Users
Create User (manual)
Loft lets you connect a variety of SSO providers for authentication but you can also manually create users who can sign in via username and password:
Create a User
Impersonate User
Loft allows admins with appropriate RBAC permissions to impersonate users.
Impersonate User
Configuration
Metadata
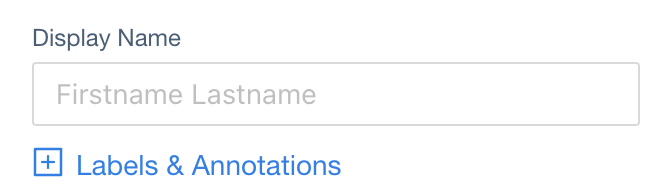
Display Name
JSONPath in User CRD:
spec.displayName (type: string)
Kubernetes Name

JSONPath in User CRD:
metadata.name (type: string)
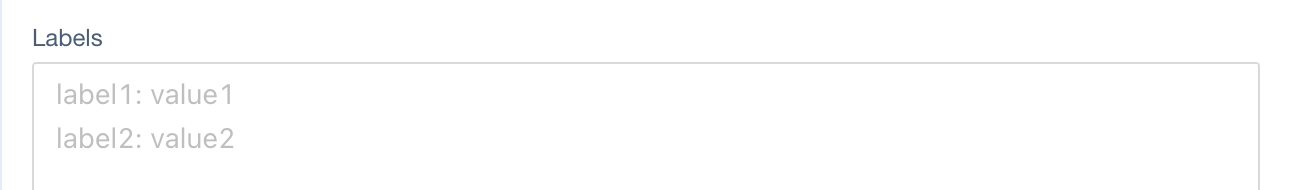
Labels
JSONPath in User CRD:
metadata.labels (type: map[string]string)
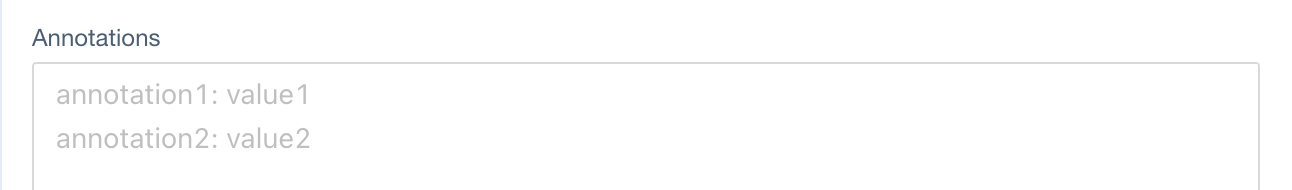
Annotations
JSONPath in User CRD:
metadata.annotations (type: map[string]string)
User Information
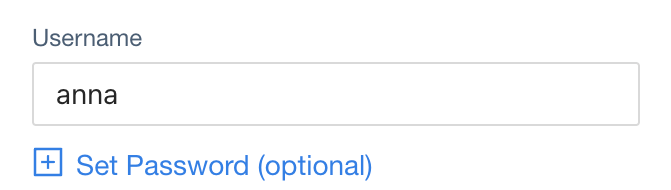
Username
JSONPath in User CRD:
spec.username (type: string)
Email
JSONPath in User CRD:
spec.email (type: string)
Password
JSONPath in User CRD:
spec.passwordRef (type: SecretRef)
Team Memberships
JSONPath in Team CRD:
$team.spec.users (type: string[])
Advanced Options
Kubernetes Groups
JSONPath in User CRD:
spec.groups (type: string[])
Cluster Roles
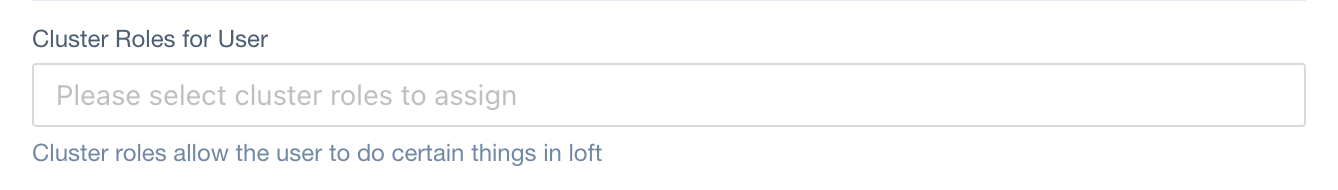
JSONPath in User CRD:
spec.clusterRoles (type: ClusterRoleRef[])
Image Pull Secrets
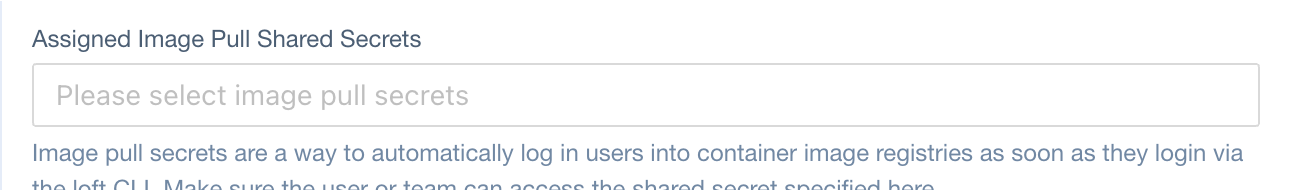
JSONPath in User CRD:
spec.imagePullSecrets (type: SecretRef[])
Access To User
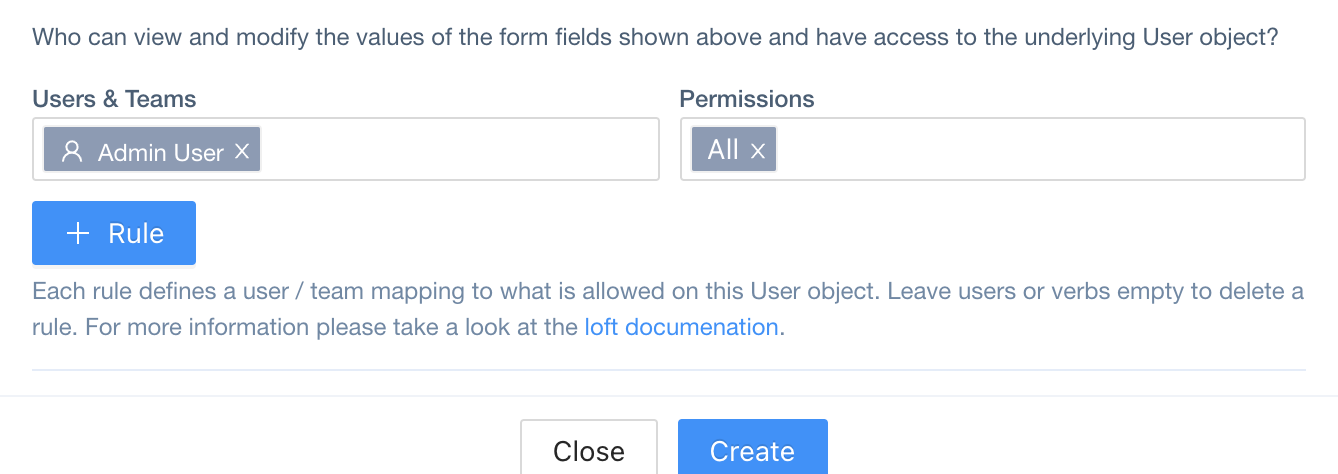
JSONPath in User CRD:
spec.access (type: Access[])
